The recent events in Spain and Portugal as well as the recent attack on UK retailers have underscored the urgent need for a detailed understanding of the risks posed by cyber terrorism to the UK, and particularly to London.
Disruptions such as widespread power outages and the targeting of critical infrastructure are stark reminders that adversaries are refining their methods and expanding their reach beyond traditional boundaries. Coupled with geopolitical tensions and persistent cyber espionage activities by state and non-state actors, these incidents highlight a multifaceted threat landscape that could have significant implications across Europe and at a global level.
TO MITIGATE THESE RISKS, ORGANISATIONS MUST ADOPT A COMPREHENSIVE SECURITY STRATEGY THAT EMBRACES BOTH PROACTIVE DEFENCE MEASURES AND THE FLEXIBILITY TO RESPOND RAPIDLY TO EMERGING THREATS.
Analysis of Major Cyber Terror Risks Impacting the UK with a Focus on London
The current threat landscape is increasingly complex, with cyber terrorism emerging as a significant concern, particularly with respect to critical infrastructure in the United Kingdom and London. Recent events, including the hacking into Marks and Spencers, Co-op and Harrods IT systems and the electrical outage that affected Spain and Portugal, have prompted organisations to reassess vulnerabilities to both cyber and physical attacks. While early assessments of the blackout ruled out a dedicated cyberattack, the incident has heightened awareness of state-sponsored strategies that may underpin broader campaigns to undermine national security and critical infrastructure resilience. This blog draws upon evidence from multiple sources and assesses the risks posed by state actors such as Iran, Russia, and China.
Overview of the Evolving Cyber Terror Threat Landscape
Cyber terrorism, as manifested by state and non-state actors alike, engages in activities ranging from espionage to outright disruption of critical infrastructure. Advances in technology – including the proliferation of inexpensive drones capable of targeted physical strikes and the increasing sophistication of remote hacking techniques – have blurred the traditional boundaries between cyber and physical warfare. The dual risk approach demonstrates that physical infrastructure, such as data centres housing sensitive information, is no longer immune to dual-mode attacks that combine covert cyber intrusion with overt physical disruption.
In addition to purely cyber-based attacks, several state actors have demonstrated a willingness to exploit vulnerabilities within national critical infrastructure. London’s central concentration of financial, transport, and communications facilities makes the city a particularly attractive target. This concentration exposes London’s dense network of data centres and critical infrastructure assets to rapid escalation in case of a coordinated attack.
State-Sponsored Motives and Methodologies
State actors such as Russia, China, and Iran have historically engaged in espionage and subversion as part of their broader geopolitical strategies. Their operations span a spectrum that includes:
- A focus on espionage and intelligence gathering via covert operations and cyber intrusions
- Disruption of economic and public service infrastructures to create uncertainty or leverage during geopolitical negotiations
- Exploitation of vulnerabilities in critical infrastructure through remote hacking, drone-based incursions, or physical intrusions
- The use of hybrid warfare tactics that blend traditional military planning with cyber tools to create ambiguity and a prolonged state of alert
Several recent trends underscore these approaches. For example, the demonstration of sophisticated cyber espionage against data centres—critical components of national infrastructure—highlights a preference for targeting locations that hold vast amounts of sensitive information and pivotal operational data. Furthermore, the potential manipulation of associated physical systems via drones further enhances attack efficacy by combining soft-target cyber methods with hard-target physical damage.
London as a High-Value Target
London’s prominence as an economic and technological hub makes it a prime target for adversaries with state-level backing. The concentration of data centres and financial institutions increases the potential for catastrophic disruption. Noteworthy points include:
- A high density of data centres, many of which are integrated into national security systems, makes London uniquely vulnerable to hybrid forms of attack.
- The locations of these centres in high-value urban settings complicate rapid physical security responses, necessitating enhanced and proactive security measures.
- Interconnectivity with international banks, government agencies, and global telecommunications providers means that any disruption in London has far-reaching implications for national and global economies.
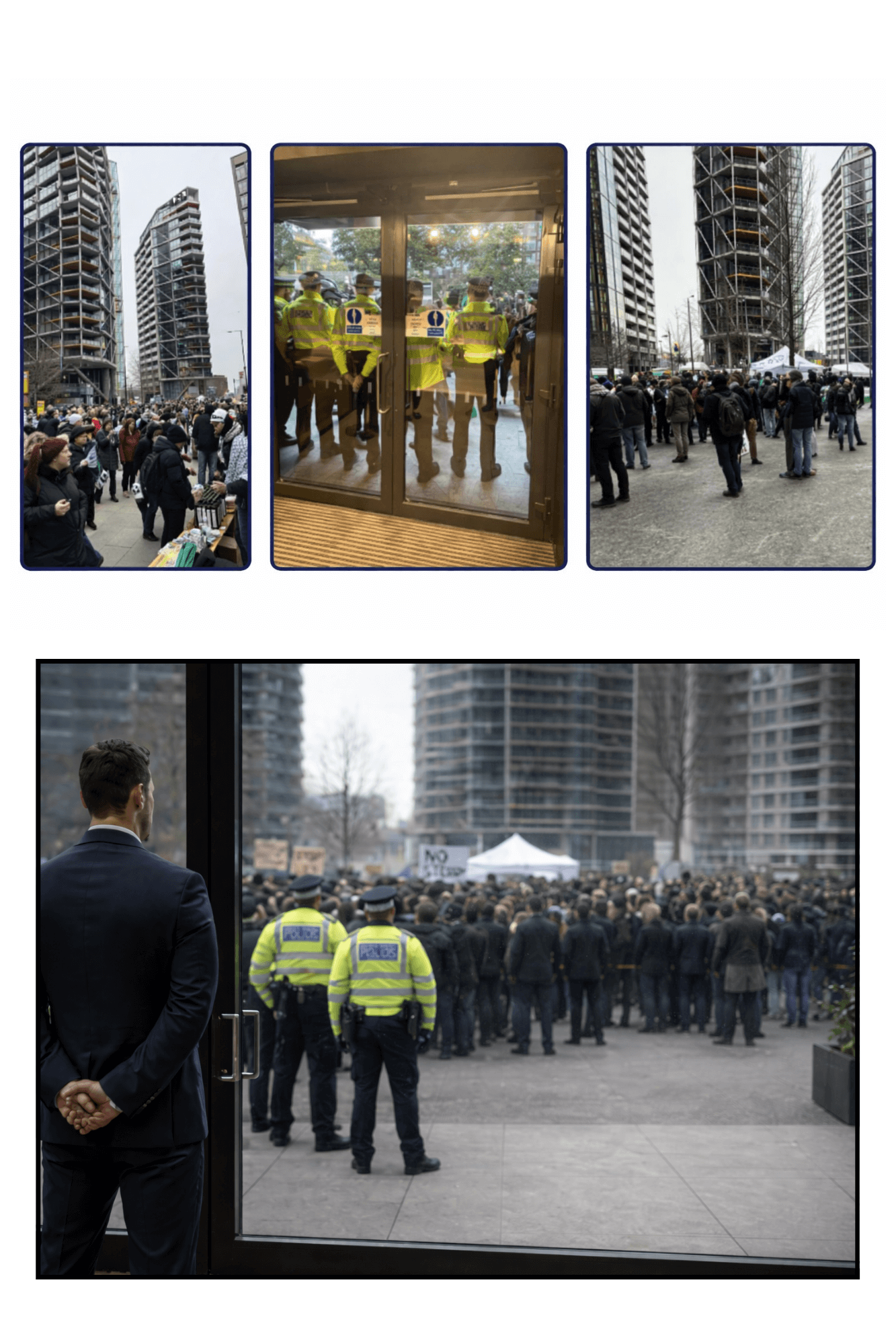
Recent enhancements in physical security protocols—such as the integration of 24-hour patrols, proactive surveillance, and rapid-response mechanisms involving SIA-licensed security teams—have mitigated some risks. Nonetheless, the evolving methods of state-sponsored cyber terrorism, which now include coordinated drone incursions coupled with electronic surveillance and remote hacking, underscore the ongoing vulnerability of London’s critical infrastructure.
Lessons from the Spain and Portugal Blackout
The recent widespread power outage in Spain and Portugal provides a timely reminder of the potential breadth of disruption if state actors exploit vulnerabilities in critical electrical grids. Although initial investigations by Spain’s grid operator have ruled out a direct cyberattack, the fact remains that such an event could have been part of a deliberate strategy involving state actors capable of leveraging both cyber and physical means.
The incident has prompted reflective analysis on several fronts:
- A significant reliance on renewable energy sources – while environmentally beneficial – presents new attack surfaces, especially if adversaries develop methods to exploit transient vulnerabilities or employ “double counting” linkages between interconnected grids.
- The possibility of secondary effects, such as disruptions to communications and satellite connectivity, exemplifies how a power outage poses more than a local inconvenience; it creates a cascade affecting critical service continuity.
- Speculation regarding third-party involvement, including possible actions by state sponsors, has raised public and governmental scrutiny across Europe. This uncertainty drives home the importance of maintaining robust physical and cyber resilience measures to deter any potential multifaceted attack.
Within the context of cyber terrorism, state actors may not seek outright destruction in a single strike but rather aim to create systemic uncertainty, weaken public confidence in institutions, and force a reassessment of national readiness. In such scenarios, a minor disturbance – such as a power outage – can be the opening gambit for a more concerted campaign against critical national infrastructure.
Risks Within Power and Energy Infrastructure
The widespread blackout that affected Spain and Portugal has shone a spotlight on the vulnerabilities within the power and energy infrastructure. Investigations into the incident indicate that the grid suffered multiple disconnection events, likely exacerbated by technical vulnerabilities and possibly compounded by external malicious influences. Although the initial assessments ruled out cyber-attacks in that specific instance, the possibility of adversaries exploiting the instability of power grids remains a significant concern for the UK.
London and other major urban centres in the UK rely on interconnected energy networks that are susceptible to similar risks. An adversary capable of coordinating a disruptive attack on the energy grid – either through coordinated hacking, the use of drones to physically interfere with power lines, or even by exploiting vulnerabilities in renewable energy systems – could precipitate widespread chaos. Such an outage would not only impact critical public services but also have far-reaching consequences for commerce, transport, and the overall security of the nation.
Implications for National and London-Specific Security Measures
The complexity of modern cyber terrorism requires that security strategies be both comprehensive and adaptive. For the United Kingdom, and London in particular, several measures are urgently needed to counter these multifaceted risks:
- Enhanced Cyber-Physical Integration: Coordination between cybersecurity teams and physical security units must be deepened. Initiatives such as real-time network access monitoring paired with on-ground physical patrols are essential in pre-empting coordinated attacks.
- Strengthened Infrastructure Audits: Regular, comprehensive reviews of all critical infrastructure—especially electrical grids, data centres, and telecommunications networks—should be mandated. Rigorous testing of penetration resistance and contingency planning plays a key role here. Recommended practices include simulated attacks, vulnerability assessments and customised protocols for response and recovery.
- Local and National Inter-Agency Collaboration: Ensuring a seamless information exchange between private security entities, law enforcement agencies, and government bodies is paramount. This collaborative environment is necessary not just for rapid disruption detection but also for coordinated responses in the event of an attack.
- Investment in Security Technologies: Adoption of advanced surveillance, threat detection systems and AI-driven monitoring tools provide a critical edge. This technology enhances the capacity not only to detect potential threats but also to identify anomalies indicative of espionage or preliminary stages of physical intrusion. Such systems must span the breadth of geographical and networked assets.
- Employee and Public Awareness: Continuous training and public advisories about the signs of potential cyber or physical breaches reinforce organisational resilience. Awareness campaigns should include guidelines on recognising phishing attempts and other social engineering tactics that often preclude more extensive operations.
London is uniquely positioned in that it faces both domestic and international scrutiny. The city’s retail, financial, and public infrastructure sectors have been increasingly targeted by state-sponsored actors employing hybrid tactics. As such, investments in next-generation security protocols, collaborative drills with emergency services and broader governmental policy enhancements are all essential to the sustained protection of these critical assets.
Strategic Considerations and Future Threat Scenarios
Looking ahead, cybersecurity experts warn that torrent-like advancements in generative artificial intelligence (genAI) and machine learning provide inherent challenges as well as opportunities for adversaries. The use of such technology not only speeds up the execution of cyber-attacks but can also be repurposed to simulate legitimate traffic or even generate convincing decoy content to obscure malicious activities.
Key strategic considerations include:
- The development of dual-layered defence strategies that combine human vigilance with the improved analytical capacity of AI-augmented systems. Such systems can scan for behaviour anomalies and intercept coordinated attempts at accessing multiple critical infrastructure points simultaneously.
- Replication of successful kinetic security protocols applied globally to high-risk areas, specifically in London. Emphasis should be placed on integrating risk-based patching, identity verification and credential protection measures with robust physical security protocols. This approach minimises the window of opportunity for adversaries.
- Increased speculative analysis of potential endpoint compromises. The evidence drawn from recent cyber espionage and cyber-terror incidents indicates that adversaries could achieve rapid lateral movement after initial intrusion. Early detection is critical to reducing ‘breakout times’, which have decreased significantly according to recent reports. With some intrusions recorded within 51 seconds, the response protocols must be similarly swift. Proactive penetration testing and regular updates to Standard Operating Procedures (SOPs) are advised to operationalise flexibility in times of acute crisis.
Moreover, adversaries may consider a multi-pronged campaign that coordinates cyber, drone-based and even electromagnetic pulse (EMP)-induced disruptions. In such scenarios, state actors would be leveraging their expansive resources and technical knowledge to initiate campaigns against various national targets. If successful, such chaotic events would have ripple effects across telecommunications, transportation and emergency services, severely undermining public and economic stability.
Internationally, the uncertainties stemming from state actor involvement in incidents like the Spain and Portugal blackout intensify the need for constant reflection on the underlying security architecture. Whether or not there is definitive evidence linking the recent outage to a state-sponsored cyber campaign, the mere possibility of such involvement has led to a realignment in risk assessments by security agencies worldwide. This has prompted calls for tighter controls, enhanced intergovernmental cooperation in intelligence sharing and increased funding dedicated to cyber and physical security infrastructure.
The Role of Collaborative Networks and Best Practices
Responding effectively to these evolving cyber terrorism risks requires robust collaborative networks. Key actions for organisations and national security bodies include:
- Establishing public-private partnerships that bring together expertise from security firms, technology providers and governmental agencies, thereby fostering a unified approach toward threat detection and mitigation.
- Following enhanced business continuity and disaster recovery plans that integrate both cyber and physical risk factors. The Business Continuity Plan document from Security Risk Specialists Ltd. outlines comprehensive strategies to respond to diverse risks—from data loss and power outages to the sudden absence of key personnel. In developing these strategies, organisations should adopt multi-layered preventive measures such as redundant networks, cloud-based data backups and rapid-response protocols.
- Engaging in regular joint exercises and simulated scenarios which not only test the efficacy of existing security systems but also help identify gaps that may be exploited by adversaries. These preparedness drills should be designed to examine potential blind spots, including those in physical access points, drone flight paths and remote intrusion detection systems.
Such collaborative strategies are particularly vital for London’s critical infrastructure, where interdependencies across financial services, transport, communications and public utilities necessitate a harmonised defensive posture. The complexity and breadth of these systems require advanced technical countermeasures and a thorough understanding of the geopolitical context that informs state-sponsored cyber terrorism. Integrating comprehensive intelligence reports, such as those from CrowdStrike and independent investigations, into daily operational planning will help develop resilience in the face of such multifaceted threats.
Implications for Policy and Future Preparedness
A key takeaway from the current cyber threat environment is the necessity for proactive policy adaptations and continuous improvement of security protocols. From a policy perspective, it is imperative that national regulators:
- Mandate regular security audits and stress-tests for critical infrastructure, particularly for facilities concentrated in high-risk areas such as London.
- Foster interagency intelligence sharing and establish rapid-response task forces dedicated to the detection and mitigation of state-sponsored cyber terrorism.
- Implement legislative frameworks to facilitate swift corrective action in the event of an attack, including protocols for financial recovery and public communications.
- Support the deployment of advanced surveillance and real-time monitoring systems that can operate across both cyber and physical domains. This includes enhancing the capacity of local security forces to identify and neutralise drone incursions and suspicious activities near key assets.
Such measures are not only critical in deterring potential state-sponsored attacks but also provide a basis for rapid recovery should an incident occur. The emphasis on real-time intelligence and quick operational response is of paramount importance, given that some adversaries can execute lateral moves within minutes. Investment in these areas is likely to yield significant dividends by limiting the scope and impact of cyber terrorism, particularly in London.
Concluding Assessment
The United Kingdom, and London in particular, are operating in an environment of elevated cyber terrorism risk, where the threat landscape is both highly complex and rapidly evolving. State actors, including Russia, China, and Iran, have demonstrated capabilities and intentions that encompass both cyber espionage and physical infrastructure disruption. Although the Spanish and Portuguese power outage has been officially ruled out as a cyber-attack, the incident underscores how vulnerable critical infrastructure remains to sophisticated, hybrid modes of attack.
In response, it is incumbent upon both public and private sectors to adopt and continually refine integrated security strategies that combine advanced cyber detection, physical security measures, and proactive intelligence collaborations. Emphasis must be placed on real-time surveillance, rapid response protocols and a resilient operational framework capable of responding to novel threat vectors powered by emerging technologies such as genAI.
London’s position as a global centre for finance, technology and governance makes it a critical national asset. Securing this asset against potential state-sponsored cyber terrorism requires not only enhanced technical and physical measures but also comprehensive policy initiatives and cross-sector collaboration. By combining lessons learned from recent incidents, such as the blackout in Spain and Portugal, with cutting-edge security practices outlined in expert documents and tested in business continuity frameworks, the UK can bolster its resilience and deter adversarial exploitation of vulnerabilities.
Ultimately, the primary objective is to safeguard critical national infrastructure, protect sensitive data centres and maintain public trust in essential services. As adversaries continue to refine their methods and accelerate the pace of their operations, a continuous cycle of improvement, policy adaptation, and operational testing will be crucial to ensure that the UK – and particularly London – remains a well-defended bastion in an increasingly volatile cyber threat landscape.
For full details of our expert Security Services, please go to: https://srslondon.co.uk/portfolio/security-guards-london/
or call us at 020 3004 4189 to find out how we are working with the UK agencies to help keep London Safe.